Hire Verified & Experienced
Encryption & Decryption Tutors
4.8/5 40K+ session ratings collected on the MEB platform
Hire The Best Encryption & Decryption Tutor
Top Tutors, Top Grades. Without The Stress!
52,000+ Happy Students From Various Universities
How Much For Private 1:1 Tutoring & Hw Help?
Private 1:1 Tutoring and HW help Cost $20 – 35 per hour* on average.
Most students fail their first encryption assignment not because the math is hard — but because nobody explained why RSA uses modular exponentiation and not just a big random number.
Encryption & Decryption Tutor Online
Encryption and decryption is the practice of converting plaintext into unreadable ciphertext using mathematical algorithms and keys, then reversing the process. It underpins data confidentiality across symmetric ciphers (AES, DES), asymmetric systems (RSA, ECC), and cryptographic protocols used in real-world security engineering.
If you’re searching for an Encryption & Decryption tutor near me, MEB connects you with verified subject specialists — tutors who have worked in Computer Science and cybersecurity at graduate and professional levels. Whether you’re working through university coursework, a security certification, or a specific module in cryptographic systems, MEB builds every session around your syllabus, your exam board, and your current gap. One tutor. One plan. Real improvement.
- 1:1 online sessions tailored to your exact course or syllabus
- Expert-verified tutors with subject-specific cryptography and security knowledge
- Flexible time zones — US, UK, Canada, Australia, Gulf
- Structured learning plan built after a diagnostic session
- Ethical homework and assignment guidance — you understand the work, then submit it yourself
52,000+ students across the US, UK, Canada, Australia, and the Gulf have used MEB since 2008 — including students in Computer Science subjects like Encryption & Decryption, cryptography, and cybersecurity.
Source: My Engineering Buddy, 2008–2025.
How Much Does an Encryption & Decryption Tutor Cost?
Most Encryption & Decryption tutoring sessions run $20–$40/hr. Graduate-level cryptography, lattice-based systems, or post-quantum encryption topics can reach $70–$100/hr depending on tutor specialisation. Start with the $1 trial — 30 minutes live or one full homework question explained — before committing to a package.
| Level / Need | Typical Rate | What’s Included |
|---|---|---|
| Undergraduate (standard modules) | $20–$35/hr | 1:1 sessions, homework guidance, concept walkthroughs |
| Graduate / Advanced Cryptography | $35–$70/hr | Expert tutor, proof-level depth, protocol analysis |
| $1 Trial | $1 flat | 30 min live session or one full homework question |
Availability tightens sharply in the weeks before finals and certification exam windows. Book early if your deadline is within four weeks.
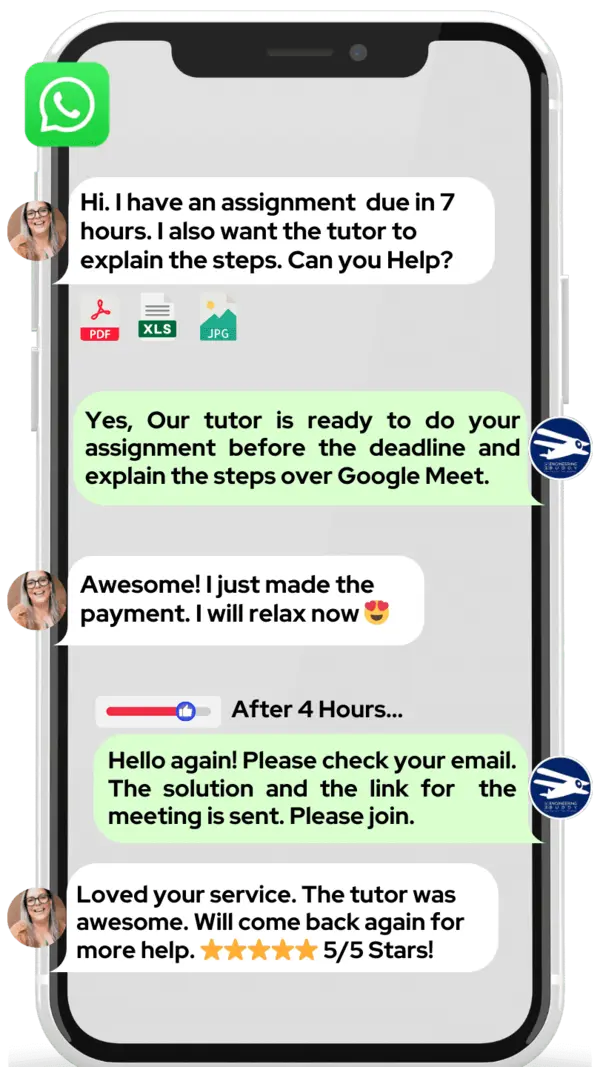
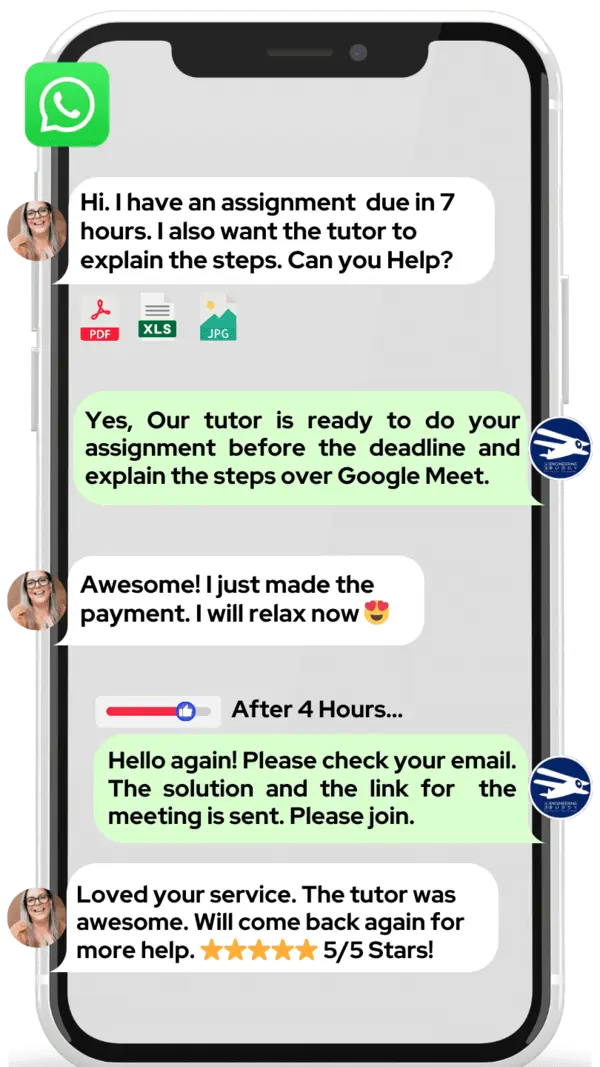
WhatsApp MEB for a quick quote — average response time under 1 minute.
Who This Encryption & Decryption Tutoring Is For
Encryption & Decryption comes up in computer science degrees, cybersecurity programmes, information security certifications, and even software engineering electives. The challenge is consistent: the topic sits at the intersection of abstract mathematics, protocol design, and implementation — and courses rarely spend enough time on all three.
- Undergraduate CS students stuck on RSA key generation, modular arithmetic, or block cipher modes
- Graduate students working through elliptic curve cryptography, zero-knowledge proofs, or lattice problems
- Students retaking after a failed first attempt — especially when the failure came down to not seeing how the maths connected to the protocol
- Students in security certifications (CompTIA Security+, CEH, CISSP) who need conceptual depth alongside exam prep
- Students with a university conditional offer depending on their final grade in a computer science or security module
- Parents supporting a second- or third-year undergraduate whose grades have dropped since encryption topics began
Students at institutions including MIT, Carnegie Mellon, University of Toronto, Imperial College London, ETH Zürich, University of New South Wales, and TU Delft have used MEB for exactly this kind of support.
1:1 Tutoring vs Self-Study vs AI vs YouTube vs Online Courses
Self-study works if your textbook is good and your maths foundation is solid — but most students discover the gap only after a failed problem set. AI tools explain AES in thirty seconds but cannot diagnose why your CBC mode implementation keeps failing. YouTube covers RSA conceptually but stops at the point where your actual assignment begins. Online courses move at a fixed pace and skip the derivations your lecturer cares about. With MEB’s 1:1 online Encryption & Decryption tutoring, the tutor works through your specific cipher implementation or proof gap live, correcting errors before they become habits. That feedback loop is what changes the grade.
Outcomes: What You’ll Be Able To Do in Encryption & Decryption
After targeted 1:1 sessions, students consistently move from memorising cipher names to actually using them. You’ll be able to apply AES in CBC and GCM modes correctly, including IV selection and padding. You’ll analyze RSA key generation step by step — choosing primes, computing the modulus, deriving the private exponent — without relying on a formula sheet you don’t understand. You’ll model a Diffie-Hellman key exchange from scratch and explain where it breaks without authentication. You’ll solve exam questions on stream ciphers, hash function properties, and digital signatures with enough depth to earn full method marks, not just the answer. And you’ll explain the difference between symmetric and asymmetric encryption in terms a technical interviewer would respect.
Based on feedback from 40,000+ sessions collected by MEB from 2022 to 2025, 58% of students improved by one full grade after approximately 20 hours of 1:1 tutoring in subjects like Encryption & Decryption. A further 23% achieved at least a half-grade improvement.
Source: MEB session feedback data, 2022–2025.
At MEB, we’ve found that students who struggle with encryption almost always have the same root problem: the modular arithmetic was never explained with actual numbers, just symbols. Once a tutor works through one full RSA example — picking primes, computing phi, finding e and d — the rest of the topic tends to click fast.
What We Cover in Encryption & Decryption (Syllabus / Topics)
Track 1: Symmetric Encryption
- Block ciphers: AES (128, 192, 256-bit), DES, and 3DES structure
- Cipher modes: ECB, CBC, CFB, OFB, CTR, and GCM — when to use each
- Stream ciphers: RC4, ChaCha20, keystream generation
- Key scheduling and round functions in AES
- Padding schemes: PKCS#7, OAEP, and their role in security
- Common implementation vulnerabilities: padding oracle attacks, IV reuse
Core texts: Applied Cryptography by Bruce Schneier; Introduction to Modern Cryptography by Katz & Lindell; Cryptography and Network Security by William Stallings.
Track 2: Asymmetric Encryption and Key Exchange
- RSA: prime generation, modular exponentiation, key derivation, CRT optimisation
- Elliptic Curve Cryptography (ECC): curve parameters, point multiplication, ECDSA
- Diffie-Hellman and ECDH key exchange protocols
- ElGamal encryption and its relationship to discrete logarithm hardness
- Digital signatures: RSA-PSS, DSA, EdDSA
- Public Key Infrastructure (PKI): certificates, CAs, chain of trust
- Post-quantum candidates: CRYSTALS-Kyber, NTRU, lattice-based systems
Core texts: A Course in Number Theory and Cryptography by Neal Koblitz; Understanding Cryptography by Paar & Pelzl; NIST post-quantum documentation from NIST.
Track 3: Cryptographic Protocols and Applied Security
- Hash functions: SHA-2, SHA-3, MD5 (weaknesses), HMAC construction
- TLS/SSL handshake: cipher suite negotiation, certificate verification, forward secrecy
- Authentication protocols: Kerberos, OAuth tokens, JWT structure and signing
- Secure key storage and management: HSMs, key derivation functions (PBKDF2, bcrypt, Argon2)
- Common protocol attacks: BEAST, POODLE, MITM, replay attacks
- End-to-end encryption design: Signal protocol, double ratchet algorithm
Core texts: Security Engineering by Ross Anderson; Cryptography Engineering by Ferguson, Schneier & Kohno; SSL/TLS tutoring pages for protocol-specific depth.
What a Typical Encryption & Decryption Session Looks Like
The tutor opens by checking the previous session’s topic — usually something like CBC mode or RSA key derivation — and asks the student to walk through one problem from memory. If anything is shaky, that gets corrected before moving on. From there, the session works through the current gap: a student might be confused about why ECC uses a finite field instead of the real numbers, or stuck on why their HMAC verification keeps failing. The tutor writes out the derivation step by step on a digital pen-pad, then hands the problem back to the student to replicate. The student explains their reasoning aloud. The tutor catches the moment where the logic breaks. By the end, the student has a concrete practice task — implement a Diffie-Hellman exchange in pseudocode, or trace through a full AES round by hand — and the next topic is already noted.
How MEB Tutors Help You with Encryption & Decryption (The Learning Loop)
Diagnose: In the first session, the tutor identifies exactly where the understanding stops. For most Encryption & Decryption students, this is one of three places: modular arithmetic, the relationship between key size and security, or the difference between confidentiality and authentication at the protocol level.
Explain: The tutor works through live problems on a digital pen-pad — not slides, not a textbook reading. A typical explanation covers one algorithm end to end: inputs, operations, outputs, and the security assumption underneath. For cryptography topics, this means showing the actual numbers, not just the notation.
Practice: The student attempts the next problem with the tutor present. For Encryption & Decryption, that might mean deriving an RSA private key from given primes, or identifying which cipher mode leaks information under a chosen-plaintext attack.
Feedback: Every error gets traced to its source — not just marked wrong. If a student’s AES implementation fails, the tutor identifies whether it’s a key schedule error, a mode confusion, or a padding misapplication. That specificity is what prevents the same mistake on the exam.
Plan: The tutor maps the next two or three topics, sets a targeted homework problem, and notes what to review at the start of the following session. Progress is tracked across sessions — not just within them.
All sessions run on Google Meet with a digital pen-pad or iPad and Apple Pencil. Before the first session, share your course syllabus or module outline, a recent assignment or past paper you struggled with, and your exam or submission date. The tutor handles the diagnostic and session plan from there. Start with the $1 trial — 30 minutes of live tutoring that also serves as your first diagnostic.
Students consistently tell us that the first session feels different from every other tutoring experience they’ve tried — because the tutor asks what they got wrong, not what topic they want to cover. Encryption & Decryption has a way of making small conceptual gaps into large exam failures. Finding the gap first changes everything.
Tutor Match Criteria (How We Pick Your Tutor)
Not every cryptography tutor is the right fit for your specific course. Here’s what MEB checks before making a match.
Subject depth: Tutors are verified for the specific level and syllabus — undergraduate security modules, graduate cryptography theory, or applied certification prep each require different expertise. A tutor who knows RSA in theory is not the same as one who can debug a TLS implementation.
Tools: Every tutor uses Google Meet with a digital pen-pad or iPad and Apple Pencil. No exceptions — Encryption & Decryption requires working through derivations in real time, not sharing static slides.
Time zone: Matched to your region — US, UK, Gulf, Canada, or Australia — so session times are sustainable, not a weekly scheduling struggle.
Goals: Whether you need exam score improvement, conceptual depth for a research project, or help with ethical hacking coursework that involves cryptographic attacks, the tutor match reflects that specific goal.
Unlike platforms where you fill out a form and wait, MEB responds in under a minute, 24/7. Tutor match takes under an hour. The $1 trial means you test before you commit. Everything runs over WhatsApp — no logins, no intake forms.
Study Plans (Pick One That Matches Your Goal)
After the diagnostic, the tutor builds a specific sequence. Three common structures: a catch-up plan (1–3 weeks) for students behind on a specific topic like asymmetric encryption or protocol security; an exam prep plan (4–8 weeks) working through past papers and weak points systematically; or ongoing weekly support aligned to your module schedule, covering new material before lectures and reinforcing it after. The plan adapts as gaps close.
Pricing Guide
Encryption & Decryption tutoring starts at $20/hr for standard undergraduate modules. Graduate-level topics — lattice-based cryptography, formal security proofs, post-quantum systems — run $35–$100/hr depending on tutor specialisation and timeline. Rate factors include course level, topic depth, urgency, and tutor availability.
For students targeting roles at cybersecurity firms, top CS graduate programmes, or FAANG-level security engineering positions, MEB can match tutors with professional industry backgrounds in applied cryptography — share your specific goal and MEB matches the tier to it.
Availability tightens significantly in the four weeks before finals. If your exam is approaching, book now rather than later.
Start with the $1 trial — 30 minutes, no registration, no commitment. WhatsApp MEB for a quick quote.
Encryption & Decryption sits at the edge of mathematics, protocol design, and implementation. Students who get it wrong on an exam usually got it wrong at one specific conceptual junction — and a single well-targeted session can close that gap before it costs marks.
Source: My Engineering Buddy, 2008–2025.
FAQ
Is Encryption & Decryption hard?
It’s genuinely difficult if your maths foundation has gaps — particularly modular arithmetic and number theory. Most students find symmetric encryption manageable but struggle with asymmetric systems and formal proofs. With a tutor working through actual examples, the difficulty drops fast.
How many sessions are needed?
Students closing a specific gap before an exam often need 4–8 sessions. Those building from scratch across a full module typically need 15–20 hours. The tutor sets a realistic estimate after the first diagnostic session.
Can you help with homework and assignments?
Yes. MEB tutoring is guided learning — you understand the work, then submit it yourself. The tutor explains the concept and method; you apply it. See our Academic Integrity policy and Why MEB page for full details on what we help with and what we don’t.
Will the tutor match my exact syllabus or exam board?
Yes. Share your course outline or module descriptor before the first session. The tutor works to your specific syllabus — not a generic encryption curriculum. This includes exam-board-specific weightings and assessment formats where relevant.
What happens in the first session?
The tutor runs a short diagnostic — asking you to explain or solve a problem from your course — to find exactly where your understanding stops. The rest of the session addresses the most urgent gap. You leave with a clear topic plan and a practice task.
Is online tutoring as effective as in-person?
For a subject like Encryption & Decryption, online is often better. The tutor writes derivations on a digital pen-pad in real time, shares screen for code walkthroughs, and the session is easy to record for review. Most students prefer it after the first session.
What’s the difference between symmetric and asymmetric encryption, and why does it matter for my exam?
Symmetric encryption uses one shared key (AES, DES). Asymmetric uses a key pair (RSA, ECC). Most exam questions test whether you understand when each is appropriate, their computational cost difference, and how they combine in protocols like TLS. Your tutor covers all three angles.
Do I need to know mathematics to understand RSA?
You need to understand modular arithmetic, Euler’s totient function, and basic prime properties — not a full number theory course. Most students can learn the necessary maths within 2–3 sessions targeted at RSA specifically. The tutor covers it as part of the cryptography explanation.
Can I get Encryption & Decryption help at midnight?
Yes. MEB operates 24/7 across time zones. WhatsApp MEB at any hour — average response time is under a minute. Sessions can be booked same-day in most cases, including evenings and weekends for US, UK, and Gulf students.
What if I don’t like my assigned tutor?
Request a different tutor via WhatsApp. MEB rematch takes under an hour. The $1 trial exists precisely so you can assess fit before spending more. If the match isn’t right, MEB fixes it — no friction, no forms.
How do I find an Encryption & Decryption tutor in my city?
All MEB sessions are online, so location doesn’t limit your options. You get access to verified tutors across the US, UK, Canada, Australia, and the Gulf — matched by subject expertise, not geography. Better tutors, more availability, no commute.
How do I get started?
Three steps: WhatsApp MEB, get matched with a verified tutor within the hour, then start your $1 trial — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment required beyond the first dollar.
Trust & Quality at My Engineering Buddy
Every MEB tutor is screened before their first session — not just for subject knowledge, but for the ability to explain it clearly under real conditions. The process includes credential review, a live demo evaluation, and ongoing feedback review after sessions. Tutors working on Encryption & Decryption hold degrees in Computer Science, Information Security, or Mathematics, and many have professional backgrounds in applied cryptography, penetration testing, or security engineering. Rated 4.8/5 across 40,000+ verified reviews on Google.
MEB tutoring is guided learning — you understand the work, then submit it yourself. For full details on what we help with and what we don’t, read our Academic Integrity policy and Why MEB.
MEB has served 52,000+ students across the US, UK, Canada, Australia, the Gulf, and Europe since 2008, covering 2,800+ subjects. In Computer Science and security, that includes students working on network protocols tutoring, malware analysis help, and distributed systems tutoring alongside Encryption & Decryption. See our tutoring methodology for how sessions are structured across all subjects.
A common pattern our tutors observe is that students who failed their first encryption exam had the algorithm memorised but not the reasoning behind it. The exam didn’t ask them to recite AES — it asked them to apply it to a scenario they hadn’t seen before. That’s a different skill, and it’s what 1:1 sessions actually build.
Explore Related Subjects
Students studying Encryption & Decryption often also need support in:
Get 1:1 online Encryption & Decryption tutoring from a verified expert — matched to your syllabus, your level, and your deadline. First session from $1.
Source: My Engineering Buddy, 2008–2025.
Next Steps
Here’s what to do right now:
- Share your exam board, module name, and the specific topic giving you trouble (RSA derivation, cipher modes, TLS protocol — be specific)
- Share your availability and time zone
- MEB matches you with a verified Encryption & Decryption tutor — usually within 24 hours, often within the hour
Before your first session, have ready: your course syllabus or module outline, a recent past paper attempt or assignment you struggled with, and your exam or deadline date. The tutor handles the rest.
Visit www.myengineeringbuddy.com for more on how MEB works.
Try your first session for $1 — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment.
WhatsApp MEB now and get matched within the hour.
WhatsApp to get started or email meb@myengineeringbuddy.com.
Reviewed by Subject Expert
This page has been carefully reviewed and validated by our subject expert to ensure accuracy and relevance.











