Hire Verified & Experienced
Metasploit Tutors
4.8/5 40K+ session ratings collected on the MEB platform
Hire The Best Metasploit Tutor
Top Tutors, Top Grades. Without The Stress!
52,000+ Happy Students From Various Universities
How Much For Private 1:1 Tutoring & Hw Help?
Private 1:1 Tutoring and HW help Cost $20 – 35 per hour* on average.
Most students who struggle with Metasploit aren’t failing because the tool is hard — they’re failing because no one has walked them through a real exploit chain, live, on their own machine.
Metasploit Tutor Online
Metasploit is an open-source penetration testing framework used to discover, exploit, and validate security vulnerabilities in systems and networks. It equips security professionals and students to conduct structured, controlled offensive security assessments.
MEB connects you with a 1:1 online Metasploit tutor who works inside the tool with you — configuring modules, walking through Meterpreter shells, and explaining every step of a real engagement workflow. If you’ve searched for a Metasploit tutor near me and hit a wall of generic cybersecurity courses, this is different. Our software engineering tutoring network includes specialists in offensive security who know Metasploit the way a pentester does — not just a lecturer who’s read the docs. You won’t just run exploit and wonder why it worked. You’ll understand why.
- 1:1 online sessions built around your specific lab environment, course, or CTF target
- Expert-vetted tutors with hands-on offensive security and penetration testing backgrounds
- Flexible time zones — US, UK, Canada, Australia, Gulf, Europe
- Structured learning plan built after a diagnostic session covering your current skill gaps
- Guided project support — we explain the technique, you run the exploit and document the findings
52,000+ students across the US, UK, Canada, Australia, and the Gulf have used MEB since 2008 — including students in Software Engineering subjects like Metasploit, Burp Suite tutoring, and Kali Linux help.
Source: My Engineering Buddy, 2008–2025.
How Much Does a Metasploit Tutor Cost?
Rates start at $20/hr for foundational Metasploit sessions and go up to $40/hr for most students. Advanced pentesting, exploit development, and evasion topics — where you need a tutor with professional red team experience — can reach $100/hr. The $1 trial gets you 30 minutes of live 1:1 tutoring or one full project question explained with context.
| Level / Need | Typical Rate | What’s Included |
|---|---|---|
| Standard (courses, CTF, labs) | $20–$35/hr | 1:1 sessions, guided project support |
| Advanced / Red Team / OSCP prep | $35–$100/hr | Expert tutor, evasion, post-exploitation depth |
| $1 Trial | $1 flat | 30 min live session or 1 project question explained |
Tutor slots fill fast during university lab deadlines and OSCP exam windows. Book early.
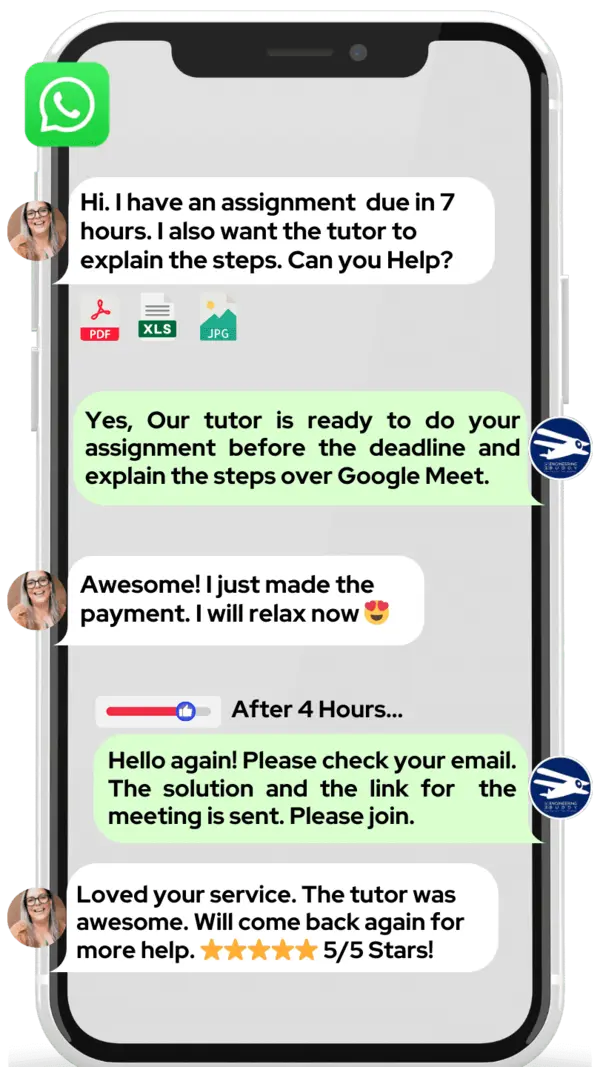
WhatsApp MEB for a quick quote — average response time under 1 minute.
Who This Metasploit Tutoring Is For
This is for anyone who’s opened Metasploit, stared at a terminal, and realised that watching a YouTube walkthrough isn’t the same as knowing what you’re doing. Whether you’re mid-course or knee-deep in a lab you can’t finish, a tutor closes that gap fast.
- Undergraduate and graduate students in cybersecurity, ethical hacking, or network security courses
- Students preparing for OSCP, CEH, or similar certifications who need live guided practice
- Students who failed a penetration testing lab or assessment and are retaking it
- Students at universities like MIT, Carnegie Mellon, Georgia Tech, University of Edinburgh, TU Delft, and UNSW working through hands-on security modules
- Self-taught security enthusiasts working toward CTF competition wins or their first bug bounty
- Students with a vulnerability assessment project due and significant technical gaps still to close
Start with the $1 trial — it doubles as your first diagnostic. You’ll know within 30 minutes whether the tutor is the right fit.
At MEB, we’ve found that Metasploit students who struggle longest are those who memorise commands without understanding the underlying protocol behaviour. One session focused on why a module works — not just how to run it — changes everything.
1:1 Tutoring vs Self-Study vs AI vs YouTube vs Online Courses
Self-study works if you have the discipline and a clear lab environment — but there’s no one to tell you why your exploit failed. AI tools explain concepts quickly but can’t watch your Meterpreter session and spot what went wrong. YouTube is excellent for overviews of specific modules, but stops the moment your target behaves differently from the video. Online courses give structure at a fixed pace with no personalisation for your specific lab or exam board. With MEB’s 1:1 online Metasploit tutor, the session is live, calibrated to your exact environment and course, and errors get caught and corrected before they become habits.
Outcomes: What You’ll Be Able To Do in Metasploit
After targeted 1:1 sessions, you’ll be able to configure and run Metasploit modules against intentionally vulnerable targets like Metasploitable and HackTheBox machines with clear purpose — not guesswork. You’ll analyze scan output from Nmap and translate it into a structured exploitation strategy using the right auxiliary and exploit modules. Apply post-exploitation techniques including Meterpreter shell navigation, privilege escalation paths, and pivoting through a compromised host. Explain your methodology in a penetration test report the way an OSCP examiner or a hiring manager actually wants to read it. Solve common failure points — payload mismatches, AV evasion, staged vs stageless payloads — without spending hours on forums.
Based on feedback from 40,000+ sessions collected by MEB from 2022 to 2025, students working 1:1 on Metasploit consistently report faster progress through lab exercises, clearer understanding of exploit chain logic, and greater confidence tackling real-world penetration testing scenarios. Progress varies by starting level and practice frequency.
Source: MEB session feedback data, 2022–2025.
Try your first session for $1 — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment. WhatsApp MEB now and get matched within the hour.
What We Cover in Metasploit (Syllabus / Topics)
Track 1: Core Framework and Exploitation Fundamentals
- Metasploit Framework architecture: msfconsole, msfvenom, msfdb
- Module types: exploits, payloads, auxiliaries, post, encoders, NOPs
- Configuring and running exploit modules against known CVEs
- Staged vs stageless payloads — when each matters and why
- Meterpreter shell basics: navigation, file system access, session management
- Vulnerability scanning with auxiliary modules and integrating Nmap output
- Targeting intentionally vulnerable systems: Metasploitable 2 and 3, DVWA
Core references: Metasploit: The Penetration Tester’s Guide (Kennedy et al.), The Hacker Playbook 3 (Kim), Rapid7 official Metasploit documentation.
Track 2: Post-Exploitation and Pivoting
- Privilege escalation on Linux and Windows via Meterpreter modules
- Credential harvesting: hashdump, Mimikatz integration, pass-the-hash
- Pivoting through a compromised host to reach internal network segments
- Persistence mechanisms and maintaining access
- Port forwarding and tunnelling using Meterpreter
- Clearing tracks: log wiping and artefact removal concepts
Core references: Penetration Testing (Weidman, No Starch Press), Advanced Penetration Testing (Allsopp), Rapid7 Metasploit Unleashed (Offensive Security).
Track 3: Evasion, OSCP Prep, and Real-World Workflows
- Antivirus evasion: encoding payloads, custom shellcode, msfvenom flags
- Firewall and IDS evasion techniques within the framework
- OSCP exam constraints — Metasploit usage rules, when you can and can’t use it
- Writing structured penetration test reports: findings, risk ratings, remediation
- CTF methodology: enumeration-first workflow, module selection logic
- Nmap tutoring for pre-exploitation reconnaissance integrated with Metasploit
Core references: The Web Application Hacker’s Handbook (Stuttard & Pinto), OSCP PWK course materials, Offensive Security official documentation.
Platforms, Tools & Textbooks We Support
Metasploit sessions run inside real environments. Tutors work with you directly on msfconsole via terminal, support Kali Linux and Parrot OS setups, and can help you configure VirtualBox or VMware lab environments for safe practice. External IEEE-aligned curriculum contexts are supported alongside university-specific lab platforms.
- Kali Linux and Parrot OS help
- VirtualBox tutoring and VMware lab environment setup
- Metasploitable 2/3, HackTheBox, TryHackMe, VulnHub
- msfvenom, msfdb, Armitage (GUI front-end)
- Wireshark, Nmap, and Burp Suite integration
- OWASP project help for web application exploitation contexts
What a Typical Metasploit Session Looks Like
The tutor opens by checking where you got stuck last time — usually a specific module that returned an unexpected error or a payload that didn’t catch. From there, you work through a target machine together on screen: the tutor watches your msfconsole output in real time, asks you to explain your module selection, and flags errors before you run the next command. If you’re working on privilege escalation, they’ll walk through the exact Meterpreter sequence while you replicate each step on your own terminal. The tutor uses a digital pen-pad to annotate the exploitation chain — showing where the vulnerability sits in the stack, what the payload is actually doing in memory. Session closes with one specific task: a named CVE to reproduce independently before next time, and the next topic queued.
How MEB Tutors Help You with Metasploit (The Learning Loop)
Diagnose: In the first session, the tutor asks you to attempt a basic exploitation task — running a known exploit against a Metasploitable target. What you struggle with tells them exactly where to start: module configuration, payload selection, post-exploitation logic, or report writing.
Explain: The tutor works through a live problem on screen using a digital pen-pad. They narrate every decision — why this exploit module, why this payload, what the LHOST and LPORT actually represent in the connection flow.
Practice: You run the next exploit. The tutor watches your commands in real time and doesn’t intervene unless you’re about to make an error that would derail the session. Productive struggle is part of the method.
Feedback: After each attempt, the tutor identifies exactly where reasoning broke down — wrong module for the service version, misconfigured handler, wrong assumption about the target OS. Not just “that’s wrong” — specifically why, and what a professional would check first.
Plan: Every session ends with the next topic named, a specific lab task assigned, and a note on what to document before the following session. Progress is tracked, not assumed.
Sessions run over Google Meet. The tutor uses a digital pen-pad or iPad with Apple Pencil to annotate exploitation diagrams and payload flow. Before your first session, share your lab environment details — OS, virtualisation setup, and the specific target or assessment you’re working toward. The first session covers a diagnostic exploit task and maps the gaps. Start with the $1 trial — 30 minutes of live tutoring that also serves as your first diagnostic.
Students consistently tell us that the moment things click in Metasploit isn’t when they get a shell — it’s when they understand why the exploit worked at the protocol level. That’s what we build toward, every session.
Tutor Match Criteria (How We Pick Your Tutor)
Not every security tutor knows Metasploit the way a working pentester does. Here’s what MEB matches on:
Subject depth: Tutors are matched by specific experience — OSCP-certified practitioners, red team professionals, and university-level offensive security instructors. Not generic “cybersecurity” tutors.
Tools: Every session runs over Google Meet with a digital pen-pad or iPad and Apple Pencil for live annotation of exploit chains and network diagrams.
Time zone: Matched to your region — US, UK, Gulf, Canada, Australia, Europe — so sessions don’t happen at 3am.
Goals: Whether you’re chasing an OSCP pass, a university lab grade, a CTF podium finish, or your first professional pentest report, the tutor is matched to that specific outcome.
Unlike platforms where you fill out a form and wait, MEB responds in under a minute, 24/7. Tutor match takes under an hour. The $1 trial means you test before you commit. Everything runs over WhatsApp — no logins, no intake forms.
Study Plans (Pick One That Matches Your Goal)
After the first diagnostic session, your tutor builds a session sequence tailored to your timeline. For students with a lab deadline in 1–3 weeks, the plan focuses on closing the specific gap — one vulnerable target, one exploitation path, done correctly. For OSCP candidates with 4–8 weeks available, sessions follow a structured progression through exploitation, post-exploitation, evasion, and report writing. For students who want ongoing support through a semester-long security course, weekly sessions align to the course syllabus and lab schedule. The tutor maps the exact sequence after your first session.
Pricing Guide
Standard Metasploit tutoring runs $20–$40/hr, covering foundational exploitation through to intermediate post-exploitation techniques. Niche topics — OSCP-level evasion, custom exploit development, red team methodology — are available at up to $100/hr with tutors who have professional red team backgrounds.
Rate factors include your experience level, the complexity of the lab environment, your timeline, and tutor availability. Slots fill quickly in the weeks before OSCP exam windows and university lab submission deadlines.
For students targeting roles at specialist security firms, government red teams, or OSCP/OSCE certification, tutors with active professional pentesting backgrounds are available at higher rates — share your specific goal and MEB will match the tier to your ambition.
Start with the $1 trial — 30 minutes, no registration, no commitment. WhatsApp MEB for a quick quote.
18 years. 52,000+ students. One platform that actually responds in under a minute when you message. MEB has been running since 2008 — that’s not a claim, that’s a track record you can check.
Source: My Engineering Buddy, 2008–2025.
FAQ
Is Metasploit hard to learn?
The interface isn’t the problem — it’s understanding what each module actually does at the network and protocol level. Students who struggle are usually missing foundational knowledge in TCP/IP, service enumeration, or OS internals. A tutor identifies which gap to close first.
How many sessions do I need?
Students closing a single lab gap typically need 2–4 sessions. OSCP candidates building complete penetration testing skills usually work across 15–25 hours of guided sessions. Your tutor maps the plan after the diagnostic.
Can you help with projects and portfolio work?
MEB provides guided project support — the tutor explains the technique and methodology, and you carry out the exploitation, document findings, and write the report yourself. MEB tutoring is guided learning; you do the work and submit it under your own name. See our policies page for full details on what we help with.
Will the tutor match my exact syllabus or exam board?
Yes. Whether your course follows an EC-Council CEH syllabus, an OSCP PWK curriculum, or a university-specific module, the tutor is matched based on that specific context — not generic cybersecurity knowledge.
What happens in the first session?
The tutor gives you a defined task — usually a specific exploit against a known vulnerable target. Your approach tells them exactly where your gaps are. The rest of the session addresses the most critical one immediately.
Is online tutoring as effective as in-person for Metasploit?
For a terminal-based tool like Metasploit, online sessions are arguably more effective — the tutor can see your exact screen, your command output, and your errors in real time. There is nothing an in-person session offers that a Google Meet session with screen share doesn’t.
Can I get Metasploit help at midnight?
Yes. MEB operates across US, UK, Gulf, and Australian time zones. WhatsApp MEB at any hour — average response time is under a minute. Tutors in your time zone are available for late-night sessions when lab deadlines hit.
What if I don’t like my assigned tutor?
Tell MEB via WhatsApp and you’ll be rematched immediately — no forms, no waiting period. The $1 trial exists precisely so you can test the match before committing to paid sessions.
How do I get started?
Three steps: WhatsApp MEB with your course or lab details, get matched to a Metasploit tutor (usually within an hour), and start your $1 trial — 30 minutes live or one project question fully explained. No registration required.
Does Metasploit work on Windows, or do I need Kali Linux?
Metasploit runs on Kali Linux, Parrot OS, and Windows. Most serious practitioners and OSCP candidates use Kali inside a VM. Your tutor will help you configure a working lab environment in your first session if needed.
What’s the difference between Metasploit Community, Pro, and the open-source Framework?
The open-source Metasploit Framework (msfconsole) is what students and OSCP candidates use — it’s free and covers all core exploitation functionality. Metasploit Pro adds a commercial GUI and automation features used in enterprise engagements. MEB tutors work with the Framework version used in your course or exam context.
Can a Metasploit tutor help me understand why an exploit failed, not just how to fix it?
That’s specifically what 1:1 tutoring does that forums and documentation can’t. Your tutor traces the failure back to the protocol, service version mismatch, or payload configuration issue — and explains the underlying reason, not just the fix.
Trust & Quality at My Engineering Buddy
Every MEB Metasploit tutor goes through a structured screening process: a live demonstration session evaluated against subject-specific criteria, verification of hands-on experience (not just credentials), and ongoing review based on student session feedback. Rated 4.8/5 across 40,000+ verified reviews on Google. Tutors covering advanced topics like evasion and post-exploitation are vetted for professional red team or practitioner experience — not just academic familiarity with the tool.
MEB provides guided learning support. All project work is produced and submitted by the student. See our Policies page for details.
MEB has served 52,000+ students across the US, UK, Canada, Australia, Gulf, and Europe in 2,800+ subjects since 2008. Within Software Engineering, that includes students working on Docker tutoring, Kubernetes help, and Metasploit — from undergraduate lab modules through to professional certification preparation. See our tutoring methodology for how sessions are structured and tutors are evaluated.
Explore Related Subjects
Students studying Metasploit often also need support in:
Next Steps
Ready to get moving? Here’s what to do:
- Share your course or certification context, the specific lab or topic you’re stuck on, and your exam or deadline date
- Share your time zone and when you’re available — morning, evening, or weekend sessions all work
- MEB matches you with a verified Metasploit tutor — usually within 24 hours, often faster
- Your first session opens with a diagnostic task so every minute is spent on your actual gap
Before your first session, have ready:
- Your lab environment details — OS, virtualisation platform, target machine
- The specific exploit attempt or lab task you struggled with most recently
- Your exam or project deadline date so the tutor can sequence the plan correctly
Visit www.myengineeringbuddy.com for more on how MEB works.
WhatsApp to get started or email meb@myengineeringbuddy.com.
A common pattern our tutors observe is this: Metasploit students who build a consistent lab practice — even 90 minutes three times a week on intentionally vulnerable targets — outperform students who study theory twice as long. The tool rewards repetition on real targets, not reading.
Reviewed by Subject Expert
This page has been carefully reviewed and validated by our subject expert to ensure accuracy and relevance.