Hire Verified & Experienced
Reverse Engineering Tutors
4.8/5 40K+ session ratings collected on the MEB platform
Hire The Best Reverse Engineering Tutor
Top Tutors, Top Grades. Without The Stress!
52,000+ Happy Students From Various Universities
How Much For Private 1:1 Tutoring & Hw Help?
Private 1:1 Tutoring and HW help Cost $20 – 35 per hour* on average.
You disassembled the binary. You ran the debugger. You still have no idea what the function actually does — and the assignment is due in 48 hours.
Reverse Engineering Tutor Online
Reverse engineering is the process of analyzing a compiled binary, hardware component, or system to recover its design, logic, or source representation — without access to original documentation — equipping practitioners with skills in disassembly, decompilation, and protocol analysis.
MEB provides 1:1 online tutoring and project help in 2800+ advanced subjects, including Reverse Engineering. If you’ve searched for a reverse engineering tutor near me and hit a wall — most generalist platforms don’t carry tutors who can work inside IDA Pro or step through shellcode — MEB does. Sessions are matched to your exact course, stack, or research goal. You work with one tutor, live, until the concept clicks. Find your software engineering tutor or jump straight into reverse engineering support below.
- 1:1 online sessions tailored to your course, CTF challenge, or research syllabus
- Expert-verified tutors with hands-on reverse engineering and binary analysis experience
- Flexible time zones — US, UK, Canada, Australia, Gulf
- Structured project plan built after a diagnostic session
- Guided project support — we explain the logic, you write the analysis
52,000+ students across the US, UK, Canada, Australia, and the Gulf have used MEB since 2008 — including students in Software Engineering subjects like Reverse Engineering, malware analysis, and vulnerability assessment.
Source: My Engineering Buddy, 2008–2025.
How Much Does a Reverse Engineering Tutor Cost?
Most reverse engineering sessions run $20–$40/hr. Highly specialized work — firmware analysis, obfuscated malware, or advanced binary exploitation — can reach $70–$100/hr. Start with the $1 trial: 30 minutes live or one project problem explained in full, no registration required.
| Level / Need | Typical Rate | What’s Included |
|---|---|---|
| Undergraduate / CTF fundamentals | $20–$35/hr | 1:1 sessions, disassembly walkthroughs, project guidance |
| Graduate / Advanced binary analysis | $35–$70/hr | Expert tutor, firmware, obfuscation, exploit development |
| $1 Trial | $1 flat | 30 min live session or one project question explained |
Tutor availability tightens significantly around university coursework deadlines and CTF competition seasons. Book early if you’re working to a fixed date.
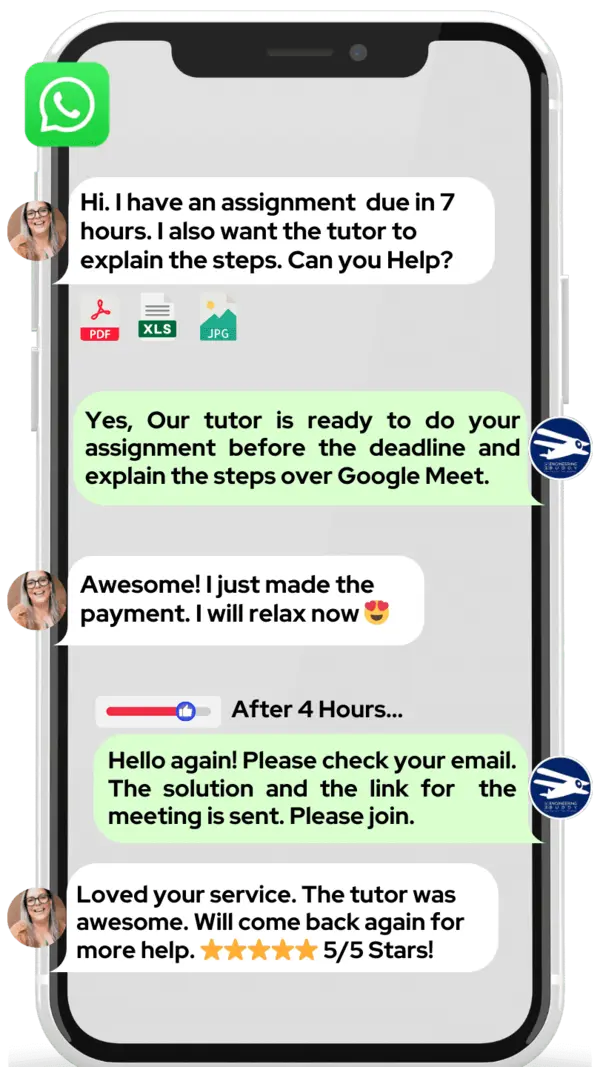
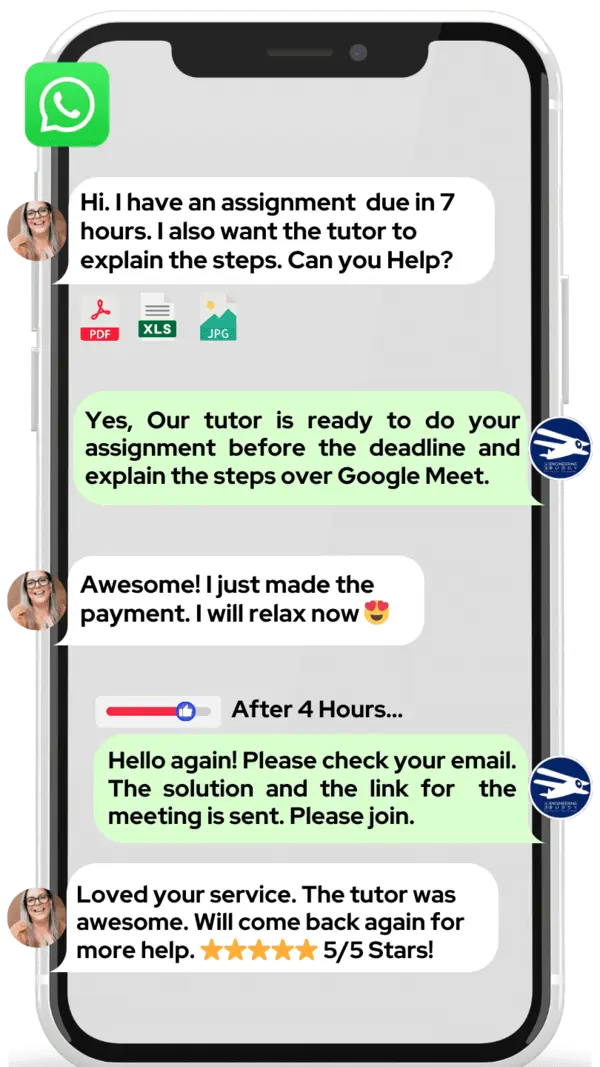
WhatsApp MEB for a quick quote — average response time under 1 minute.
Who This Reverse Engineering Tutoring Is For
Reverse engineering sits at an uncomfortable intersection: it requires assembly language literacy, OS internals knowledge, and analytical patience — all at once. Most students hit a wall not because they lack ability, but because they’ve never had someone walk them through a real binary step by step.
- Undergraduate CS or cybersecurity students tackling their first binary analysis assignment
- Graduate and PhD students working on malware research, firmware extraction, or protocol reverse engineering
- CTF competitors stuck on a pwn or reversing challenge with a deadline approaching
- Students who failed a binary exploitation or systems security module and need to retake
- Security professionals preparing for certifications that include reverse engineering components (OSCP, GREM)
- Students at MIT, Carnegie Mellon, Georgia Tech, Stanford, ETH Zürich, Imperial College London, and TU Delft who need specialist support beyond office hours
If you’re 4–6 weeks from a submission or exam with real gaps in your disassembly or decompilation skills, the $1 trial is the fastest way to see exactly where you stand.
At MEB, we’ve found that reverse engineering students often know more than they think — they just haven’t seen a tutor reason aloud through a real binary. One session of watching an expert narrate their thought process changes how students approach every problem after.
1:1 Tutoring vs Self-Study vs AI vs YouTube vs Online Courses
Self-study works if you’re disciplined, but reverse engineering without feedback means reinforcing wrong mental models for weeks. AI tools explain concepts quickly but can’t step through your specific binary or adapt when your approach is subtly wrong. YouTube is excellent for tool overviews — GDB basics, IDA navigation — but stops dead when you hit an obfuscated function no tutorial covers. Online courses give structure but move at a fixed pace, and most skip the edge cases that actually appear in coursework. 1:1 tutoring with MEB is live, calibrated to your exact binary or assignment, and corrects your reasoning in real time — which matters most in a subject where one wrong assumption sends the entire analysis off track.
Outcomes: What You’ll Be Able To Do in Reverse Engineering
After working with an MEB reverse engineering tutor, you’ll be able to analyze x86 and x64 assembly output and reconstruct the original C-equivalent logic. You’ll apply static and dynamic analysis techniques using tools like IDA Pro, Ghidra, and GDB to identify function boundaries, calling conventions, and data structures. You’ll solve CTF reversing and pwn challenges methodically rather than by trial and error. You’ll explain anti-analysis techniques — packing, obfuscation, anti-debugging — and describe how to work around them. And you’ll present findings in a structured technical report, the format most university modules and professional roles actually require.
Based on feedback from 40,000+ sessions collected by MEB from 2022 to 2025, 58% of students improved by one full grade after approximately 20 hours of 1:1 tutoring in subjects like Reverse Engineering. A further 23% achieved at least a half-grade improvement.
Source: MEB session feedback data, 2022–2025.
Try your first session for $1 — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment.
WhatsApp MEB now
and get matched within the hour.
What We Cover in Reverse Engineering (Syllabus / Topics)
Track 1: Static Analysis and Disassembly
- x86 and x64 assembly fundamentals — registers, stack frames, calling conventions
- Disassembly with IDA Pro and Ghidra — navigating functions, cross-references, and data segments
- Identifying control flow: loops, conditionals, and switch tables in compiled code
- String and import analysis — reconstructing high-level behavior from artifacts
- Symbol recovery and type inference in stripped binaries
- Compiler optimizations and how they affect readability of disassembled output
Core references: Practical Malware Analysis (Sikorski & Honig), Hacking: The Art of Exploitation (Erickson), IDA Pro documentation.
Track 2: Dynamic Analysis and Debugging
- Setting up controlled analysis environments — VMs, snapshots, network isolation
- Dynamic debugging with GDB, x64dbg, and WinDbg — breakpoints, memory inspection, stepping
- Behavioral analysis — system calls, file I/O, registry access, network traffic
- Unpacking and dumping — identifying packers, triggering OEP, reconstructing IAT
- Anti-debugging detection and bypass — IsDebuggerPresent, timing checks, TLS callbacks
- Heap sprays, use-after-free scenarios, and memory corruption identification
Core references: The Art of Memory Forensics (Ligh et al.), Malware Analyst’s Cookbook (Ligh et al.), GDB documentation.
Track 3: Exploit Development and CTF Reversing
- Buffer overflow exploitation — stack-based and heap-based, return address control
- ROP chain construction — gadget identification with ROPgadget and pwntools
- Format string vulnerabilities — read and write primitives, GOT overwrite
- CTF reversing challenges — crackmes, keygen problems, obfuscated algorithms
- ASLR, NX/DEP, and stack canaries — understanding mitigations and bypass strategies
- Writing clean exploit scripts in Python using pwntools
Core references: The Shellcoder’s Handbook (Koziol et al.), Reversing: Secrets of Reverse Engineering (Eilam), pwntools documentation.
What a Typical Reverse Engineering Session Looks Like
The tutor opens by checking the previous topic — usually whichever assembly construct or debugging step the student flagged as unclear. From there, the student shares their screen showing the binary loaded in Ghidra or IDA Pro, and the tutor walks through the function together, narrating the reasoning: what the register state tells us, why the compiler generated this particular sequence, and where the interesting logic actually lives. The tutor uses a digital pen-pad to annotate the disassembly directly, drawing stack diagrams and marking data flow. The student then replicates the analysis on a related function, explaining their reasoning aloud while the tutor listens and corrects. The session closes with a concrete task — analyze a specific section of a provided crackme, or reproduce a buffer overflow in a controlled sample — and the next topic is noted before the call ends.
How MEB Tutors Help You with Reverse Engineering (The Learning Loop)
Diagnose: In the first session, the tutor asks the student to attempt a simple disassembly task from scratch. This reveals immediately whether the gaps are in assembly literacy, tool navigation, or analytical reasoning — each requires a different fix.
Explain: The tutor works through a representative binary live, narrating every decision. Problems are chosen to match the student’s exact course or challenge type — not generic textbook examples that won’t appear in their actual assessment.
Practice: The student attempts the next binary or challenge with the tutor present and silent until the student gets stuck. This is where real learning happens — not in watching, but in attempting.
Feedback: The tutor walks back through the student’s reasoning step by step. When something was wrong, the tutor explains exactly which assumption failed and why — not just what the correct answer is.
Plan: After each session the tutor notes which constructs the student handles confidently and which need another pass. The sequence for subsequent sessions is set before the call ends.
Sessions run over Google Meet with a digital pen-pad or iPad plus Apple Pencil. Before the first session, share your course outline or assignment brief, any binary samples or CTF links, and your deadline. The first session starts with the diagnostic task and ends with a clear plan. Start with the $1 trial — 30 minutes of live tutoring that also serves as your first diagnostic.
Students consistently tell us that reverse engineering finally clicked when a tutor reasoned through a real binary out loud — not through slides. The moment they see the decision-making process narrated live, the assembly stops looking like noise.
Tutor Match Criteria (How We Pick Your Tutor)
Not every software or security tutor can reverse engineer a stripped binary. MEB matches on four criteria:
Subject depth: Tutors are verified on the specific area — static analysis, dynamic debugging, exploit development, or firmware — matching your course or research goal precisely.
Tools: Every tutor works over Google Meet with a digital pen-pad or iPad plus Apple Pencil — annotation is not optional in this subject, it’s how the analysis gets explained.
Time zone: Matched to your region — US, UK, Gulf, Canada, or Australia — so sessions don’t require anyone to be awake at 3 a.m.
Goals: Whether you’re closing a gap before a systems security exam, working through a CTF, or doing graduate research on firmware, the tutor is selected for that specific outcome.
Unlike platforms where you fill out a form and wait, MEB responds in under a minute, 24/7. Tutor match takes under an hour. The $1 trial means you test before you commit. Everything runs over WhatsApp — no logins, no intake forms.
Study Plans (Pick One That Matches Your Goal)
The tutor builds a specific sequence after the diagnostic — but most students fall into one of these tracks. Catch-up (1–3 weeks): closing specific gaps before a submission deadline, covering one or two key constructs per session. Exam or CTF prep (4–8 weeks): systematic coverage of static analysis, dynamic debugging, and exploitation techniques with timed practice problems. Weekly support: ongoing sessions aligned to coursework deadlines or research milestones throughout the semester. The tutor maps the exact session plan after the first diagnostic.
Pricing Guide
Reverse engineering tutoring starts at $20/hr for undergraduate-level binary analysis and CTF fundamentals. Graduate-level work — firmware extraction, advanced obfuscation, exploit chain development — typically runs $50–$100/hr depending on tutor specialization and timeline pressure.
Rate factors: academic level, topic complexity (stripped binaries cost more tutor time than standard assignments), urgency, and tutor availability. Demand spikes during university finals and major CTF competition seasons — if you have a fixed deadline, book as early as possible.
For students targeting roles at top security firms, government research labs, or graduate programs at institutions with strong systems security tracks, tutors with professional penetration testing or malware research backgrounds are available at higher rates — share your specific goal and MEB will match the tier to your ambition.
Start with the $1 trial — 30 minutes, no registration, no commitment. WhatsApp MEB for a quick quote.
FAQ
Is reverse engineering hard?
Yes — it requires assembly literacy, OS internals knowledge, and methodical reasoning simultaneously. Most students find it hard not because it’s impossible but because no one has walked them through a real binary start to finish. That’s exactly what MEB sessions do.
How many sessions are needed?
Students covering one specific gap — a single assembly construct or debugging technique — typically need 3–5 sessions. A full static and dynamic analysis skill-build from scratch usually takes 15–25 sessions, depending on starting level and practice between meetings.
Can you help with projects and portfolio work?
MEB provides guided project support. The tutor explains the logic, walks through the analysis approach, and helps you understand why each step works. The analysis, write-up, and submission are yours. MEB tutoring is guided learning — you understand the work, then submit it yourself. See our Academic Integrity policy and Why MEB page for full details on what we help with and what we don’t.
Will the tutor match my exact syllabus or exam board?
Yes. Share your course outline, module description, or assignment brief before the first session. The tutor is matched to your specific content — not a generic reverse engineering curriculum that might differ from what your university or certification program actually assesses.
What happens in the first session?
The tutor gives you a short diagnostic task — typically analyzing a simple binary or explaining a given assembly snippet. This locates exactly where your gaps are. The rest of the session starts building from that point, and a structured plan is set before the call ends.
Are online lessons as effective as in-person?
For reverse engineering, yes — and in some ways better. Screen sharing means the tutor sees exactly what you see in your disassembler. Digital annotation directly on the binary output is often clearer than whiteboard diagrams. Students at MIT and Georgia Tech use MEB online successfully alongside their in-person coursework.
What tools do I need installed before my first session?
Ghidra or IDA Free covers most undergraduate and CTF work and both are free to install. For dynamic analysis, GDB on Linux or x64dbg on Windows. The tutor confirms the exact setup needed when you book — there’s no single universal environment for this subject.
Can MEB help with CTF challenges specifically?
Yes. CTF reversing and pwn challenges are a specific area MEB tutors cover — including crackmes, keygen problems, heap exploitation, and ROP chain construction. Share the challenge link or binary and the tutor works through the approach with you rather than just handing over a solution.
Can I get reverse engineering help at midnight?
MEB operates 24/7 via WhatsApp. Message any time — average response is under a minute. Session scheduling depends on tutor time zone alignment, but the initial contact and match process runs around the clock, which matters when a CTF ends at 2 a.m.
What if I don’t understand my tutor’s approach?
Tell MEB within the first session. A replacement tutor is arranged promptly. The $1 trial exists specifically so there’s no financial risk in discovering the fit isn’t right before committing to ongoing sessions.
What’s the difference between IDA Pro and Ghidra, and which should I learn first?
Ghidra is free and more accessible — a solid starting point for most students. IDA Pro is the industry standard in professional malware analysis and security research. Your tutor will recommend based on your course requirements or career direction, and can work fluently in either.
How do I get started?
Message MEB on WhatsApp with your binary, course outline, or challenge description. MEB matches you with a verified reverse engineering tutor — usually within an hour. Your first session is the $1 trial: 30 minutes live, no registration, no commitment. Three steps: WhatsApp → matched → start trial.
Trust & Quality at My Engineering Buddy
Every MEB tutor goes through a subject-specific vetting process — not a generic interview. For reverse engineering, that means demonstrating live disassembly, explaining a stripped binary’s logic, and completing a practical exercise on the tools students actually use. Tutors hold relevant degrees in computer science, cybersecurity, or electrical engineering, and many have professional backgrounds in penetration testing, malware research, or embedded systems security. Ongoing session feedback is reviewed, and tutors who don’t meet quality standards after student feedback are removed. Rated 4.8/5 across 40,000+ verified reviews on Google.
MEB tutoring is guided learning — you understand the work, then submit it yourself. For full details on what we help with and what we don’t, read our Academic Integrity policy and Why MEB.
MEB has been running since 2008, serving 52,000+ students across the US, UK, Canada, Australia, the Gulf, and Europe in 2,800+ subjects. Within Software Engineering, tutors cover Reverse Engineering alongside subjects like software testing, code optimization, and binary exploitation. For a full picture of how MEB selects and trains tutors, see our tutoring methodology.
The SANS Institute has documented how practical, hands-on instruction accelerates technical skill acquisition in cybersecurity subjects — a principle that underpins MEB’s live 1:1 approach to reverse engineering education.
Source: SANS Institute Reading Room.
A common pattern our tutors observe is that students who struggle with reverse engineering have the right tools installed but no mental model for how to start. Teaching that starting heuristic — where to look first in any unknown binary — is often the most valuable thing a single session delivers.
Explore Related Subjects
Students studying Reverse Engineering often also need support in:
Next Steps
Before your first session, have ready: your exam board and syllabus (or course outline), any binary samples or CTF challenge links you’re working on, a recent assignment you struggled with, and your exam or deadline date. The tutor handles the rest.
- Share your course outline, hardest topic, and current timeline
- Share your availability and time zone
- MEB matches you with a verified reverse engineering tutor — usually within an hour
- First session starts with a diagnostic so every minute is used well
Visit www.myengineeringbuddy.com for more on how MEB works.
WhatsApp to get started or email meb@myengineeringbuddy.com.
Reviewed by Subject Expert
This page has been carefully reviewed and validated by our subject expert to ensure accuracy and relevance.