Hire The Best Parrot OS Tutor
Top Tutors, Top Grades. Without The Stress!
52,000+ Happy Students From Various Universities
How Much For Private 1:1 Tutoring & Hw Help?
Private 1:1 Tutoring and HW help Cost $20 – 35 per hour* on average.
Most students trying to learn Parrot OS for pentesting hit the same wall: they can run the tools but have no idea what the output means.
Parrot OS Tutor Online
Parrot OS is a Debian-based Linux distribution built for cybersecurity, digital forensics, and privacy. It includes pre-installed penetration testing tools, a hardened kernel, and a lightweight MATE desktop environment aimed at security professionals and researchers.
If you’re searching for a Parrot OS tutor near me, the sessions are fully online — same live, 1:1 format regardless of whether you’re in the US, UK, Canada, Australia, or the Gulf. MEB connects you with verified tutors who work across software engineering and security-focused disciplines, including Parrot OS itself. Your tutor diagnoses exactly where you’re stuck — not just which tool, but why the output isn’t making sense — and builds sessions around that.
- 1:1 online sessions tailored to your specific Parrot OS workflow and goals
- Expert verified tutors with hands-on cybersecurity and Linux experience
- Flexible time zones — US, UK, Canada, Australia, Gulf
- Structured project support — we explain, you build
- Guided project support — we explain, you execute every step yourself
52,000+ students across the US, UK, Canada, Australia, and the Gulf have used MEB since 2008 — including students in Software Engineering subjects like Parrot OS, Kali Linux tutoring, and Metasploit help.
Source: My Engineering Buddy, 2008–2025.
How Much Does a Parrot OS Tutor Cost?
Most Parrot OS sessions run $20–$40/hr depending on the depth you need — beginner Linux navigation through to advanced exploitation frameworks. The $1 trial gets you 30 minutes of live 1:1 tutoring or one full walkthrough of a problem you’re stuck on.
| Level / Need | Typical Rate | What’s Included |
|---|---|---|
| Standard (most levels) | $20–$35/hr | 1:1 sessions, guided project support |
| Advanced / Specialist | $35–$70/hr | Expert tutor, deep pentesting or forensics focus |
| $1 Trial | $1 flat | 30 min live session or 1 project question |
Tutor availability tightens in the weeks before university project submission deadlines and certification exam windows. Book early if your timeline is tight.
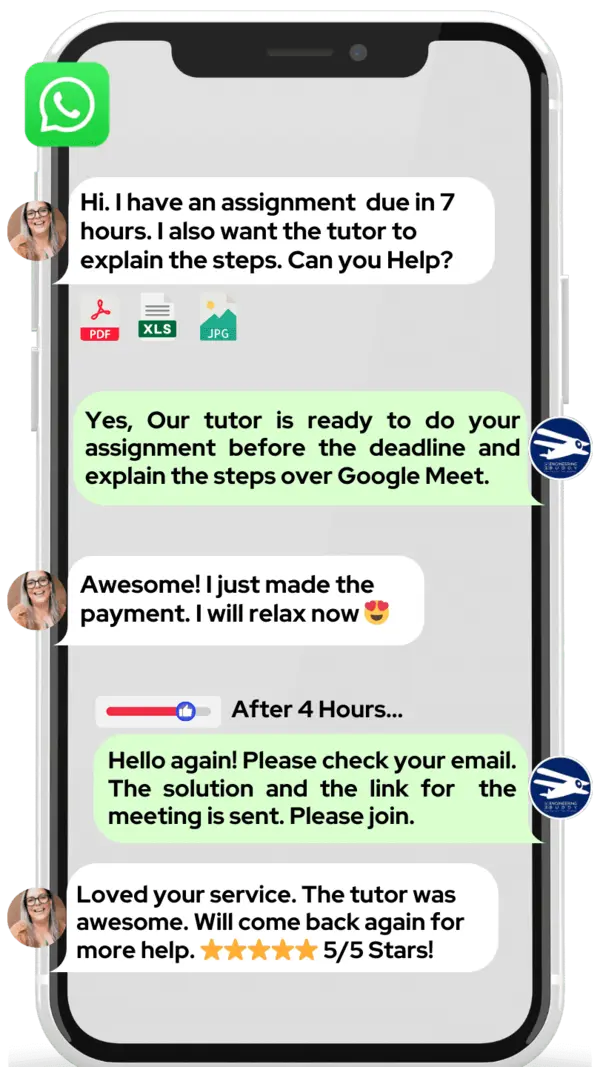
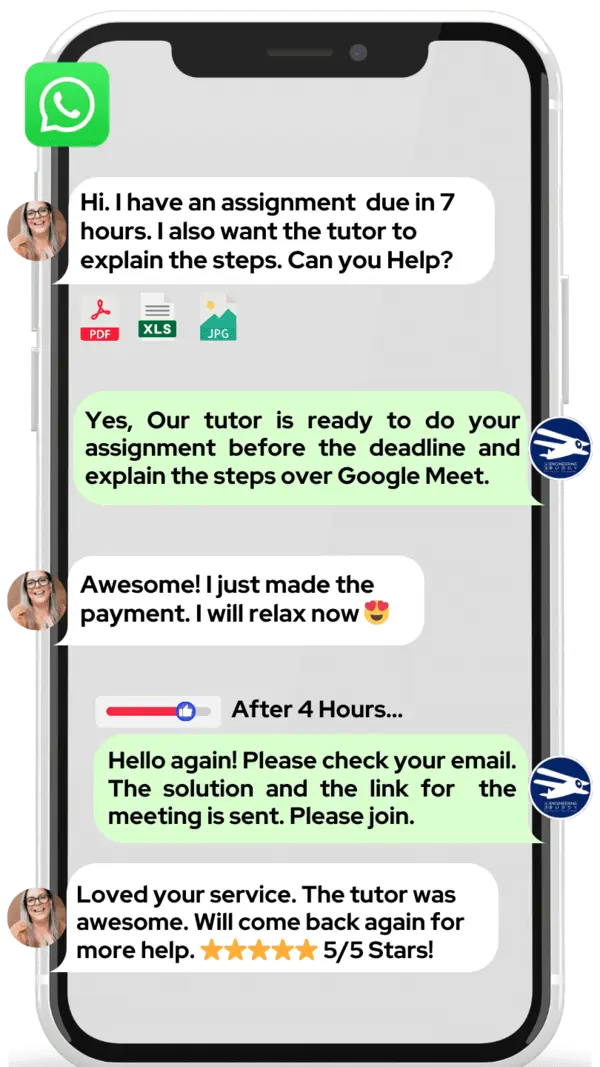
WhatsApp MEB for a quick quote — average response time under 1 minute.
Who This Parrot OS Tutoring Is For
This isn’t a course for absolute beginners who’ve never opened a terminal. It works best for students who have some Linux exposure and are now hitting real obstacles — tools that won’t run, output they can’t interpret, or lab environments they can’t configure.
- Undergraduate and postgraduate cybersecurity students working through hands-on lab assignments
- Students pursuing CEH, OSCP, CompTIA Security+, or similar certifications who need live guidance, not just video walkthroughs
- Students whose university project depends on setting up a working Parrot OS environment and running a full penetration test
- Students who failed a security lab or practical assessment and need to retake with a solid understanding of what went wrong
- Developers shifting into DevSecOps or security roles who need to get up to speed on the toolset fast
- Students at universities including Georgia Tech, Carnegie Mellon, University of Edinburgh, TU Delft, and University of Toronto who include Linux-based security tools in their security curricula
The $1 trial is a practical way to test whether the tutor-student fit is right before committing to a full schedule.
1:1 Tutoring vs Self-Study vs AI vs YouTube vs Online Courses
Self-study works if you know exactly which gaps to fill — rare in a tool-heavy subject like Parrot OS. AI tools give you command syntax fast, but can’t watch you misread a Nmap scan and correct you in real time. YouTube covers installations well; it stops when your specific environment breaks. Online courses move at a fixed pace whether you’re stuck on ARP poisoning or already past it. With a 1:1 Linux tutor from MEB, every session is calibrated to your exact Parrot OS workflow — the tutor sees your screen, spots the error, and explains the fix before you’ve lost the thread.
Outcomes: What You’ll Be Able To Do in Parrot OS
After consistent 1:1 sessions, you’ll be able to set up and configure a Parrot OS environment from scratch, including network interface and VPN settings. You’ll be able to run and interpret Nmap reconnaissance scans accurately — not just execute the command but read the output. You’ll be able to apply Metasploit modules against a target in a controlled lab setting, understanding each stage of the exploit chain. Analyse packet captures in Wireshark and identify anomalies that matter. Present a structured penetration test report covering scope, methodology, findings, and remediation steps — the kind that satisfies a university marker or a professional client brief.
Based on feedback from 40,000+ sessions collected by MEB from 2022 to 2025, 58% of students improved by one full grade after approximately 20 hours of 1:1 tutoring in subjects like Parrot OS. A further 23% achieved at least a half-grade improvement.
Source: MEB session feedback data, 2022–2025.
MEB provides guided learning support. All project work is produced and submitted by the student. See our Policies page for details.
What We Cover in Parrot OS (Syllabus / Topics)
Track 1: Environment Setup and Linux Fundamentals
- Installing Parrot OS on VirtualBox, VMware, or bare metal
- Terminal navigation: file system, permissions, user management
- Package management with APT and managing tool updates
- Network interface configuration: static IP, wireless adapters, VPN setup
- Bash scripting basics for automating repetitive security tasks
- Using the Parrot OS MATE desktop and switching between security and home editions
Recommended references: The Linux Command Line by William Shotts; Linux Basics for Hackers by OccupyTheWeb — both cover terminal and scripting fundamentals applicable to Parrot OS sessions.
Track 2: Penetration Testing and Exploitation
- Reconnaissance with Nmap — scan types, flag interpretation, OS fingerprinting
- Vulnerability scanning with OpenVAS and Nikto
- Exploitation with Metasploit — selecting modules, setting payloads, post-exploitation basics
- Password attacks with Hydra and Hashcat against controlled lab targets
- Web application testing: SQL injection, XSS identification using OWASP ZAP and Burp Suite help
- Wireless network auditing with Aircrack-ng in a legal lab environment
- Writing structured penetration test reports: scope, methodology, CVSS scoring, remediation
Recommended references: Penetration Testing by Georgia Weidman; The Web Application Hacker’s Handbook by Stuttard and Pinto — both are standard lab companions for this track. The National Institute of Standards and Technology publishes cybersecurity frameworks tutors align lab goals to.
Track 3: Digital Forensics and Incident Response
- Disk imaging with dd and Guymager — write-blocking principles
- File recovery and metadata extraction using Autopsy and Foremost
- Memory forensics with Volatility — process listing, network connections, artefact extraction
- Network traffic analysis in Wireshark — protocol dissection, anomaly identification
- Log analysis and correlation for basic incident response scenarios
- Chain of custody documentation and forensic report writing standards
Recommended references: Digital Forensics with Open Source Tools by Altheide and Carvey; The Art of Memory Forensics by Ligh et al. — both map directly to Parrot OS forensics toolset used in university modules.
At MEB, we’ve found that students stuck on Parrot OS aren’t usually struggling with the tools themselves — they’re struggling with what the output is telling them. A tutor who has run these assessments professionally reads that output differently. That’s the gap a 30-minute session can start to close.
Platforms, Tools & Textbooks We Support
Parrot OS sessions are inherently tool-heavy. Tutors work directly with the tools students have installed and help troubleshoot configuration, usage, and output interpretation across the full security stack. The following are commonly supported in sessions:
- Parrot OS Security Edition and Home Edition
- VirtualBox and VMware Workstation for lab environments
- Nmap, Netcat, Nessus, OpenVAS
- Metasploit Framework, Armitage
- Burp Suite Community and Professional
- Wireshark, tcpdump
- Autopsy, Volatility, Foremost, Guymager
- Aircrack-ng, Hashcat, Hydra, John the Ripper
- GNS3 for network simulation alongside Parrot OS lab setups — see GNS3 tutoring
What a Typical Parrot OS Session Looks Like
The tutor opens by checking what you attempted since last session — usually a specific Nmap scan, a Metasploit module run, or a Wireshark capture you were asked to interpret. You share your screen. If the scan returned unexpected output or the exploit failed to land, the tutor walks through the exact command flags and target configuration to find where the logic broke. They use a digital pen-pad to annotate the terminal output live — circling the port states that matter, marking the service version that changes your next move. Then you replicate it. You run the corrected command while the tutor watches. The session closes with a defined task: a specific lab challenge on a named target, a section of a penetration test report to draft, or a forensics exercise with Autopsy. The next topic is agreed before the call ends.
How MEB Tutors Help You with Parrot OS (The Learning Loop)
Diagnose: In the first session, the tutor asks you to walk through the last thing you attempted — exactly what command you ran, what output you got, what you expected. That’s usually enough to identify whether the gap is environmental (misconfigured network adapter, wrong Parrot edition) or conceptual (misreading scan states, not understanding the exploit chain).
Explain: The tutor works through a live example on a legal lab target — narrating every decision. Why this scan type. Why this module. What this output means and what to do next. The digital pen-pad annotates the terminal in real time so nothing is abstract.
Practice: You run it. Same environment, same tool, same target. The tutor watches for the moment the reasoning slips — that’s where the real correction happens, not after the fact.
Feedback: Errors are corrected step by step, with explanation of why a wrong flag choice or misread output would cost you in an assessed lab or a real engagement. Specific. No vague encouragement.
Plan: Each session ends with a defined next topic, a practice task with a measurable outcome, and a note of what to flag if it goes wrong before next session.
Sessions run over Google Meet. The tutor uses a digital pen-pad or iPad with Apple Pencil to annotate terminal output and diagrams live. Before your first session, have your Parrot OS environment running — even if it’s broken, that’s useful — and a specific task or error you’re stuck on. First session covers diagnostic and first working run-through together. Start with the $1 trial — 30 minutes of live tutoring that also serves as your first diagnostic.
Students consistently tell us that the first time a tutor annotates their terminal output in real time — pointing to exactly which line is wrong and why — something clicks that hours of documentation reading hadn’t managed. That moment is what we design every Parrot OS session around.
Tutor Match Criteria (How We Pick Your Tutor)
Not every Linux tutor is right for Parrot OS. The match matters.
Subject depth: Tutors have hands-on experience with Parrot OS Security Edition specifically — not just general Linux. They’ve run penetration tests, built forensics labs, and understand the toolset at a practical level, not just a theoretical one.
Tools: Every session runs over Google Meet with a digital pen-pad or iPad and Apple Pencil. Tutors can annotate your terminal output and lab diagrams in real time.
Time zone: Matched to your region — US, UK, Gulf, Canada, Australia — so evening sessions are genuinely available when you need them.
Goals: Whether you need to pass a university practical, build a portfolio project, or prepare for OSCP-style lab environments, the tutor match is calibrated to that specific goal — not a one-size approach.
Unlike platforms where you fill out a form and wait, MEB responds in under a minute, 24/7. Tutor match takes under an hour. The $1 trial means you test before you commit. Everything runs over WhatsApp — no logins, no intake forms.
Pricing Guide
Parrot OS tutoring starts at $20/hr for foundational Linux and environment setup. Penetration testing and digital forensics sessions with specialist tutors typically run $35–$70/hr. Graduate-level or professional certification preparation can reach up to $100/hr depending on tutor background and subject depth.
Rate factors: your current level, the specific tools and topics covered, how close your deadline is, and tutor availability in your time zone. Availability narrows in the 4–6 weeks before major university submission windows — plan ahead if you’re working to a fixed date.
For students targeting roles at firms like Deloitte Cyber, KPMG Advisory, or CrowdStrike, or pursuing OSCP and GPEN certifications, tutors with professional penetration testing backgrounds are available at higher rates — share your specific goal and MEB will match the tier to your ambition.
Start with the $1 trial — 30 minutes, no registration, no commitment. WhatsApp MEB for a quick quote.
FAQ
Is Parrot OS hard to learn?
It’s not beginner-friendly if you’ve never used Linux. The tools assume you understand networking and the command line. With a tutor who corrects your gaps live rather than letting you guess from documentation, the learning curve compresses significantly — most students see real progress within 3–5 sessions.
How many sessions will I need?
Depends on your starting point and goal. Students with basic Linux experience targeting a university practical typically need 6–10 sessions. Those starting from scratch or working toward a structured certification lab environment usually need 15–20. The diagnostic first session gives a clearer projection.
Can you help with projects and portfolio work?
Yes. MEB tutoring is guided learning — the tutor explains the methodology, walks through the tool usage, and helps you understand what your results mean. You run the tools, you write the report, you submit your own work. MEB does not complete assessments on your behalf. See our Academic Integrity policy and Why MEB page for full details on what we help with and what we don’t.
Will the tutor match my exact syllabus or exam board?
Yes. When you message MEB, share your course name, university module code if you have one, and any specific tools or lab environments listed on your syllabus. The tutor match is built around that — not a generic security curriculum that may not align with your assessment requirements.
What happens in the first session?
The tutor asks you to walk through what you’ve already attempted and what broke. From that, they map the gaps — environmental, conceptual, or tool-specific — and you work through a first live example together. You leave with a specific practice task and a clear plan for sessions 2 onwards.
Are online sessions as effective as in-person for Parrot OS?
For a tool-heavy subject like Parrot OS, online is often more practical. You’re working in your own lab environment — the one that’s actually broken — while the tutor annotates your screen in real time. There’s nothing an in-person session offers here that a Google Meet session with screen sharing doesn’t match or exceed.
What’s the difference between Parrot OS Security Edition and the Home Edition — and which one do I need for tutoring?
Security Edition includes the full suite of pre-installed penetration testing and forensics tools. Home Edition is a general-purpose Linux desktop without the security toolset. For any cybersecurity course or lab assignment, you need Security Edition. MEB tutors help you confirm which edition your course requires and get it configured correctly from the first session.
Is Parrot OS better than Kali Linux for learning penetration testing?
Both run similar toolsets. Parrot OS is generally considered lighter on system resources and includes stronger built-in privacy features. Kali Linux has a larger community and more third-party documentation. Your university or certification programme may specify one — if not, a tutor can help you choose based on your hardware and goals. MEB covers both; see also Kali Linux tutoring if your programme uses that distribution instead.
Can I get Parrot OS help at midnight or on weekends?
Yes. MEB operates across time zones 24/7. Students in the Gulf, Australia, and the US West Coast regularly book late-evening or weekend slots. WhatsApp MEB with your availability and time zone — a tutor match happens in under an hour regardless of when you message.
What if I don’t like my assigned tutor?
Request a change over WhatsApp. MEB rematch is free and fast — under an hour in most cases. The $1 trial exists precisely so you test the fit before committing to a full schedule. If the tutor isn’t right, you haven’t lost anything significant.
How do I get started?
Three steps: WhatsApp MEB with your course, current Parrot OS setup, and the specific problem you’re trying to solve. MEB matches you with a verified tutor — usually within the hour. Your first session is the $1 trial — 30 minutes live or one full project question explained in detail.
Trust & Quality at My Engineering Buddy
Every MEB tutor goes through a structured vetting process: subject knowledge screening, a live demo session evaluated by senior staff, and ongoing review based on student feedback after each session. Tutors covering Parrot OS hold degrees or professional experience in cybersecurity, computer science, or digital forensics — and have practical, hands-on background with the specific tools your course requires. Rated 4.8/5 across 40,000+ verified reviews on Google.
MEB provides guided learning support. All project work is produced and submitted by the student. For full details on what we help with and what we don’t, read our Academic Integrity policy and Why MEB.
MEB has been running since 2008, serving 52,000+ students across the US, UK, Canada, Australia, Gulf, and Europe in 2,800+ subjects. Within Software Engineering and cybersecurity, that includes Parrot OS, vulnerability assessment tutoring, Nmap help, and OWASP tutoring — tutors matched to your specific tool stack, not a generic security overview.
Try your first session for $1 — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment. WhatsApp MEB now and get matched within the hour.
18 years of operation, 52,000+ students served, and a 4.8/5 rating across 40,000+ reviews — MEB has been the platform security and engineering students reach for when a deadline is real and a gap needs closing fast.
Source: My Engineering Buddy, 2008–2025.
Explore Related Subjects
Students studying Parrot OS often also need support in:
- Reverse Engineering
- DevOps
- Docker
- Ansible
- Fedora Linux
- Embedded Linux
- Certified Information Systems Auditor (CISA)
A common pattern our tutors observe is that students who struggle with Parrot OS have solid theoretical knowledge from lectures but have never had someone sit with them through a full tool run-through in a live environment. That’s the gap MEB closes — not re-explaining theory, but making the practice actually work.
Next Steps
Ready to get unstuck on Parrot OS? Here’s what to do:
- Share your course name, the specific Parrot OS tool or topic you’re blocked on, and your deadline
- Share your time zone and availability — morning, evening, or weekend slots all work
- MEB matches you with a verified tutor — usually within 24 hours, often within the hour
- First session starts with a diagnostic so every minute is used on the right problem
Before your first session, have ready:
- Your course outline or module guide listing the tools and assessments
- Your current Parrot OS setup details — edition, whether it’s in a VM, any errors you’re hitting
- Your project brief, lab sheet, or the specific task you’re working on
The tutor handles the rest.
Visit www.myengineeringbuddy.com for more on how MEB works.
WhatsApp to get started or email meb@myengineeringbuddy.com.
Reviewed by Subject Expert
This page has been carefully reviewed and validated by our subject expert to ensure accuracy and relevance.