Hire Verified & Experienced
Kali Linux Tutors
4.8/5 40K+ session ratings collected on the MEB platform
Hire The Best Kali Linux Tutor
Top Tutors, Top Grades. Without The Stress!
52,000+ Happy Students From Various Universities
How Much For Private 1:1 Tutoring & Hw Help?
Private 1:1 Tutoring and HW help Cost $20 – 35 per hour* on average.
Most students who struggle with Kali Linux aren’t bad at security — they’ve never had someone walk them through a real penetration test, tool by tool, live on screen.
Kali Linux Tutor Online
Kali Linux is a Debian-based Linux distribution built for penetration testing, digital forensics, and security research. It ships with 600+ pre-installed security tools, equipping students and professionals to conduct structured vulnerability assessments and ethical hacking tasks.
Finding a reliable Kali Linux tutor near me is harder than it sounds — most platforms don’t distinguish between general Linux help and hands-on offensive security training. MEB does. Our software engineering tutoring network includes verified Kali Linux specialists who work through real lab scenarios with you, live, covering Nmap scans, Metasploit modules, Burp Suite intercepts, and custom exploit scripting — not just theory. One session with the right tutor changes how fast you move through the rest of your course.
- 1:1 online sessions tailored to your course syllabus or certification track
- Expert-verified tutors with hands-on penetration testing and forensics experience
- Flexible time zones — US, UK, Canada, Australia, Gulf
- Structured learning plan built after a diagnostic session
- Guided project support — we explain the technique, you run the tool and document the findings
52,000+ students across the US, UK, Canada, Australia, and the Gulf have used MEB since 2008 — including students in Software Engineering subjects like Kali Linux, Metasploit tutoring, and Nmap help.
Source: My Engineering Buddy, 2008–2025.
How Much Does a Kali Linux Tutor Cost?
Most Kali Linux sessions run $20–$40/hr. Specialist tutors covering advanced exploit development, red team operations, or OSCP-aligned lab work are priced higher — up to $100/hr. Not sure yet? The $1 trial gets you 30 minutes of live, hands-on tutoring before you spend anything more.
| Level / Need | Typical Rate | What’s Included |
|---|---|---|
| Standard (course/bootcamp level) | $20–$35/hr | 1:1 sessions, tool walkthroughs, project guidance |
| Advanced / OSCP / Red Team | $35–$100/hr | Expert tutor, exploit scripting, CTF and lab prep |
| $1 Trial | $1 flat | 30 min live session or one project question explained |
Tutor availability tightens sharply around CEH and OSCP exam windows and end-of-semester lab submission deadlines. Book early if you’re on a fixed timeline.
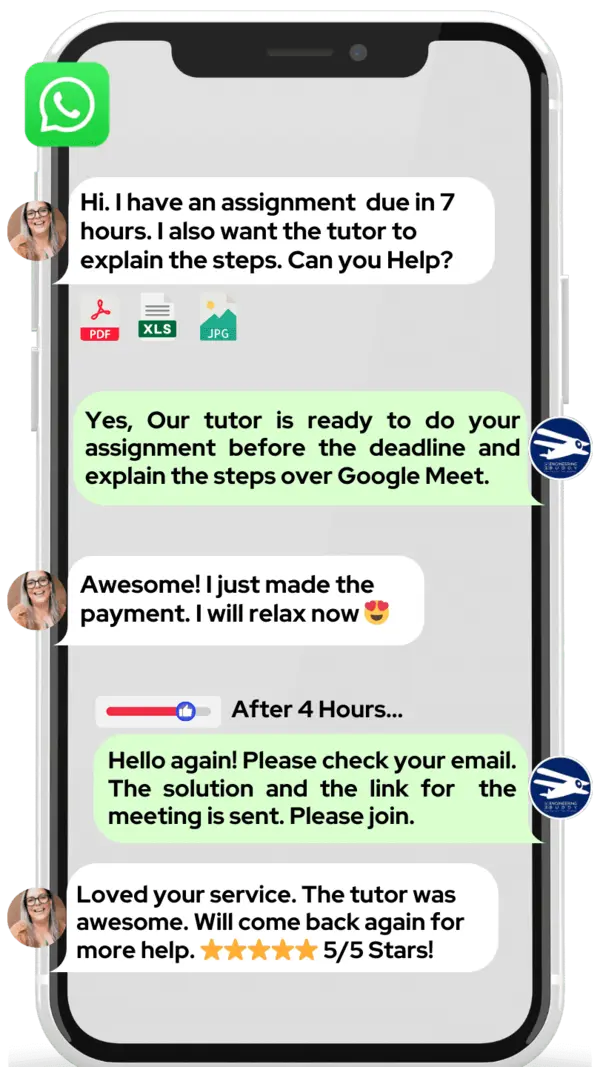
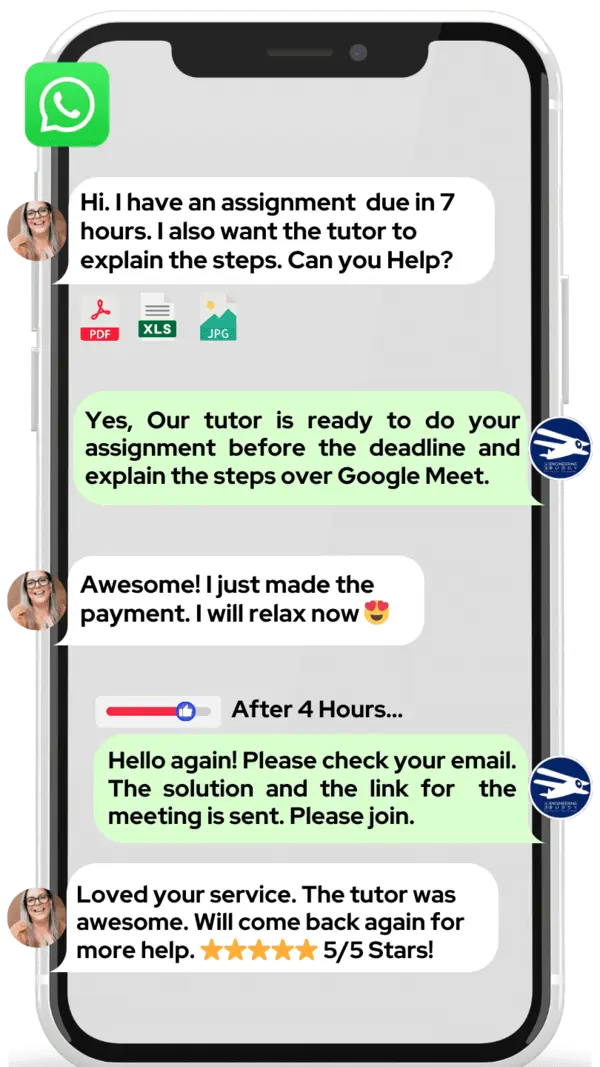
WhatsApp MEB for a quick quote — average response time under 1 minute.
Who This Kali Linux Tutoring Is For
Some students open Kali Linux for the first time and freeze — 600 tools, a terminal that expects precision, and no obvious starting point. Others are mid-course and can run basic scans but can’t string a full engagement together. Both situations are solvable in a few focused sessions.
- Undergraduate and graduate students in cybersecurity, computer science, or network engineering courses that require Kali Linux lab work
- Students preparing for the OSCP, CEH, eJPT, or CompTIA PenTest+ certifications
- Students who failed a lab submission or practical assessment and need to understand what went wrong
- Students with a coursework or lab submission deadline approaching — and significant gaps still to close
- Developers and IT professionals learning offensive security for the first time through a bootcamp or self-directed path
- Students at institutions including Georgia Tech, Purdue, UC San Diego, Carnegie Mellon, University of Toronto, and Imperial College London who carry Kali Linux modules in their security curricula
Try the $1 trial if you’re not sure where to start — the first session is also a diagnostic.
1:1 Tutoring vs Self-Study vs AI vs YouTube vs Online Courses
Self-study works if you’re disciplined, but Kali Linux has no feedback loop when your Nmap flags are wrong or your payload doesn’t fire. AI tools explain concepts quickly but can’t watch you misconfigure a listener and catch it live. YouTube is useful for overviews — it stops when your specific lab environment behaves differently. Online courses are structured but fixed-pace, and security labs vary enormously by instructor. 1:1 tutoring with MEB is live, matched to your exact course or cert track, and corrects errors the moment they appear — which in Kali Linux is the only way to actually learn what’s happening inside the tool.
Outcomes: What You’ll Be Able To Do in Kali Linux
After focused 1:1 sessions, students can run a full reconnaissance phase using Nmap and Netdiscover against a target network, enumerate services and identify exploitable vulnerabilities, apply relevant Metasploit modules or manual exploits, intercept and manipulate web traffic using Burp Suite, and write structured penetration test reports that document methodology, findings, and remediation steps. Students also develop the habit of working inside a controlled lab environment — using VirtualBox or VMware alongside Kali — so their methodology is clean, repeatable, and defensible in an assessment context.
Based on feedback from 40,000+ sessions collected by MEB from 2022 to 2025, students working 1:1 on Kali Linux consistently report faster progress through lab exercises, stronger confidence with command-line tool chains, and clearer understanding of how to structure a full penetration testing engagement from reconnaissance to reporting. Progress varies by starting level and practice frequency.
Source: MEB session feedback data, 2022–2025.
At MEB, we’ve found that Kali Linux students plateau at the same point: they can run individual tools in isolation but can’t chain them into a coherent engagement. The tutor’s job in the first two sessions is almost always to bridge that gap — not to teach more tools, but to show how the ones you already know connect.
What We Cover in Kali Linux (Syllabus / Topics)
Track 1: Reconnaissance and Enumeration
- Passive reconnaissance — OSINT techniques using theHarvester and Maltego
- Active scanning with Nmap — flags, service detection, OS fingerprinting
- Network discovery using Netdiscover and ARP scanning
- Service enumeration with Gobuster, Enum4linux, and SMBclient
- DNS enumeration and zone transfer attempts
- Writing structured reconnaissance reports from tool output
Core references: The Web Application Hacker’s Handbook (Stuttard & Pinto), Penetration Testing (Georgia Weidman), Nmap tutoring resources.
Track 2: Exploitation and Post-Exploitation
- Vulnerability identification with OpenVAS and Nikto
- Exploit selection and staging using Metasploit help — msfconsole, search, use, set, run
- Manual exploit development — buffer overflows, shellcode basics
- Post-exploitation: Meterpreter sessions, privilege escalation paths
- Password cracking with Hashcat and John the Ripper
- Maintaining access — persistence mechanisms and covering tracks
Core references: Hacking: The Art of Exploitation (Jon Erickson), The Hacker Playbook 3 (Peter Kim), vulnerability assessment tutoring.
Track 3: Web Application Testing and Wireless Security
- Web app testing methodology — OWASP Top 10 applied in practice
- Intercepting and modifying HTTP/S traffic with Burp Suite project help
- SQL injection, XSS, CSRF testing against lab environments
- Wireless security — WPA2 cracking with Aircrack-ng, handshake capture
- Social engineering simulation using SET (Social Engineering Toolkit)
- Writing professional pentest reports — CVSS scoring, remediation recommendations
Core references: The Web Application Hacker’s Handbook, OWASP tutoring, Kali Linux Revealed (Hertzog, O’Gorman & Aharoni).
Platforms, Tools & Textbooks We Support
Kali Linux sessions run inside real tool environments — not slides. Tutors work directly with you in the following setups and support any platform your course or cert track requires:
- Kali Linux (bare metal, VMware, VirtualBox, WSL2)
- Metasploit Framework and Armitage
- Burp Suite Community and Professional
- Nmap, Wireshark, Aircrack-ng, Hashcat, John the Ripper
- TryHackMe, Hack The Box, VulnHub lab environments
- VirtualBox tutoring and VMware project help for lab setup
- GNS3 for network simulation alongside Kali — see GNS3 tutoring
What a Typical Kali Linux Session Looks Like
The tutor opens by checking the previous topic — usually whether the student successfully ran a Nmap scan and correctly interpreted the output. From there, the session moves to the current block: today that might be configuring a Metasploit listener, staging a payload against a VulnHub machine, or walking through a failed privilege escalation attempt to find where the path broke. The tutor uses a digital pen-pad to annotate the terminal output in real time — circling the relevant flag, marking the misconfigured parameter. The student then replicates the step and explains why each command was chosen. The session closes with a specific task: run the same technique against a second machine and document the outcome before next time.
Students consistently tell us that the biggest shift in Kali Linux happens when they stop copying commands and start reading what the tool actually returns. Once that clicks — usually around session three or four — the rest of the toolset opens up fast.
How MEB Tutors Help You with Kali Linux (The Learning Loop)
Diagnose: In the first session, the tutor identifies exactly where the student is stuck — whether that’s terminal navigation, tool syntax, lab environment setup, or conceptual gaps in how TCP/IP relates to what Nmap is doing. Generic gaps show up immediately.
Explain: The tutor works through the technique live — running the tool, narrating each step, annotating output with a digital pen-pad. Nothing is assumed. Every flag, every module parameter gets a reason.
Practice: The student takes over. Same tool, same target, different machine. The tutor stays on screen and watches — not to intervene immediately, but to let the student work through initial hesitation before stepping in.
Feedback: When something breaks — wrong flag, missed port, failed exploit — the tutor walks back through the output line by line. The student identifies the error. The tutor explains why that error costs marks in an assessed lab and what the correct approach looks like.
Plan: The session ends with a concrete next step: a specific machine on TryHackMe or Hack The Box to attempt before the next session, with a particular technique to practice. The tutor notes where to pick up next time.
All sessions run over Google Meet. Tutors use a digital pen-pad or iPad with Apple Pencil to annotate terminal output, diagrams, and network maps in real time. Before your first session, share your course outline or certification track, a recent lab you struggled with, and your deadline. The first session covers the diagnostic and the first technique block — no time is wasted on setup.
Start with the $1 trial — 30 minutes of live tutoring that also serves as your first diagnostic.
Try your first session for $1 — 30 minutes of live 1:1 tutoring or one homework question explained in full. No registration. No commitment. WhatsApp MEB now and get matched within the hour.
Tutor Match Criteria (How We Pick Your Tutor)
Not every security tutor knows Kali Linux at the lab level. Here’s what MEB screens for:
Subject depth: Hands-on penetration testing experience, not just familiarity with security concepts. Tutors are matched by certification track (OSCP, CEH, CompTIA PenTest+) or by course syllabus if university-based.
Tools: Sessions run on Google Meet with digital pen-pad or iPad plus Apple Pencil — tutor annotates your terminal output live, not just talks over slides.
Time zone: Matched to your region — US East and West, UK, Gulf, Canada, Australia. No awkward 3am calls.
Goals: Whether you need to pass a lab practical, clear a certification exam, or build project depth for a portfolio role at firms like CrowdStrike, Palo Alto Networks, or Deloitte’s cyber practice — the tutor match accounts for that.
Unlike platforms where you fill out a form and wait, MEB responds in under a minute, 24/7. Tutor match takes under an hour. The $1 trial means you test before you commit. Everything runs over WhatsApp — no logins, no intake forms.
MEB has been matching students with verified, subject-specific tutors since 2008 — across Linux tutoring, DevOps project help, and hands-on security tools like Kali Linux. The match isn’t random — it’s based on your exact tool stack and timeline.
Source: My Engineering Buddy, 2008–2025.
Pricing Guide
Standard Kali Linux tutoring runs $20–$40/hr, covering course-level and bootcamp students. OSCP-aligned lab work, red team methodology, and advanced exploit development are priced $40–$100/hr, depending on tutor background and session intensity.
Rate factors: your current level, which tools and techniques the sessions need to cover, how close your deadline is, and tutor availability. Specialist tutors with professional red team backgrounds book out fast during OSCP and CEH exam periods.
For students targeting roles at top security firms or pursuing OSCP certification, tutors with active penetration testing or red team backgrounds are available at higher rates — share your specific goal and MEB will match the tier to your ambition.
Start with the $1 trial — 30 minutes, no registration, no commitment. WhatsApp MEB for a quick quote.
FAQ
Is Kali Linux hard to learn?
The tools themselves aren’t the hard part — understanding what they’re telling you is. Students with a basic Linux command-line background and some networking knowledge typically make fast progress. Without those foundations, two or three sessions of targeted groundwork closes the gap.
How many sessions will I need?
Most students need 6–12 sessions to cover a full penetration testing workflow from reconnaissance to reporting. Targeted help for a single lab submission or one failing component can resolve in 2–3 sessions. The tutor maps a specific plan after the first diagnostic.
Can you help with projects and portfolio work?
Yes. MEB provides guided learning support — the tutor explains the technique and methodology, walks through the tool chain with you, and helps you understand the output. All lab work and documentation is produced and submitted by you. See our Academic Integrity policy and Why MEB page for full details on what we help with and what we don’t.
Will the tutor match my exact syllabus or certification track?
Yes. Share your course outline, certification path (OSCP, CEH, eJPT, CompTIA PenTest+), or lab platform (TryHackMe, Hack The Box, VulnHub) before the first session. MEB matches a tutor who has worked with that specific content — not a generalist.
What happens in the first session?
The tutor runs a diagnostic — checking your current tool familiarity, where your last lab broke down, and what your deadline looks like. From there, the session moves straight into the first technique block. You leave with a specific practice task and a clear map of what comes next.
Are online Kali Linux sessions as effective as in-person?
For terminal-based work, often more so. The tutor shares your screen, annotates output live with a digital pen-pad, and can take over briefly to demonstrate — something that’s harder to do cleanly in person. Students consistently report that the live screen-share format works well for tool-heavy sessions.
Can I get Kali Linux help late at night or on weekends?
Yes. MEB tutors cover US, UK, Gulf, and Australia time zones — sessions are available across most hours, including evenings and weekends. WhatsApp response time averages under a minute around the clock. If your lab is due Monday morning, message Saturday night.
What if I don’t get on with my assigned tutor?
Tell MEB after the first session. No friction, no explanation required. A different tutor with the same subject depth gets matched — usually within a few hours. The $1 trial is specifically designed so you test the fit before committing to a full block of sessions.
Do you help with CTF (Capture the Flag) challenges?
Yes. CTF prep is one of the most common Kali Linux requests MEB handles. Tutors work through challenge categories — web exploitation, binary exploitation, forensics, cryptography — using the same tool chain as a real pentest. CTF experience also builds the skills needed for OSCP lab machines.
What is the difference between Kali Linux and Parrot OS for security work?
Both are Debian-based security distributions with overlapping tool sets. Kali Linux is more widely used in professional and certification contexts — OSCP labs run on it by default. Parrot OS tutoring is lighter on system resources and suits students on lower-spec machines. MEB tutors work with both; specify which your course requires.
How do I get started?
Message MEB on WhatsApp, share your course or cert track, and start the $1 trial — 30 minutes of live tutoring or one project question explained in full. Three steps: WhatsApp → matched within the hour → start your trial session.
Trust & Quality at My Engineering Buddy
Every MEB tutor goes through screening before taking a session — subject-knowledge check, live demo evaluation, and ongoing feedback review after each session. Kali Linux tutors are verified for hands-on penetration testing experience, not just theoretical security knowledge. Rated 4.8/5 across 40,000+ verified reviews on Google.
MEB tutoring is guided learning — you understand the work, then submit it yourself. For full details on what we help with and what we don’t, read our Academic Integrity policy and Why MEB.
MEB has served 52,000+ students across the US, UK, Canada, Australia, the Gulf, and Europe in 2,800+ subjects since 2008. The Software Engineering and cybersecurity subject area covers reverse engineering tutoring, CISA certification help, and the full Kali Linux tool chain — not just introductory content. Read more about how sessions are structured at our tutoring methodology page.
MEB tutors have supported students through OSCP prep, university security lab modules, and CEH exam revision since 2008 — across embedded Linux project help, cloud architecture tutoring, and offensive security disciplines including Kali Linux.
Source: My Engineering Buddy, 2008–2025.
Explore Related Subjects
Students studying Kali Linux often also need support in:
Next Steps
Share your certification track or course module, the specific tool or technique you’re stuck on, and your deadline. MEB matches you with a verified Kali Linux tutor — usually within an hour.
- Share your exam board, hardest component, and current timeline
- Share your availability and time zone
- MEB matches you with a verified tutor — usually within 24 hours
Before your first session, have ready: your course outline or certification path (OSCP, CEH, eJPT), a recent lab you struggled with or a specific tool output you couldn’t interpret, and your deadline date. The tutor handles the rest.
Visit www.myengineeringbuddy.com for more on how MEB works.
WhatsApp to get started or email meb@myengineeringbuddy.com.
Reviewed by Subject Expert
This page has been carefully reviewed and validated by our subject expert to ensure accuracy and relevance.













